Blog about hosting and servers

There are no new features in this version, there are only about 40 improvements. Some of these improvements guarantee a smoother upgrade to version 5.
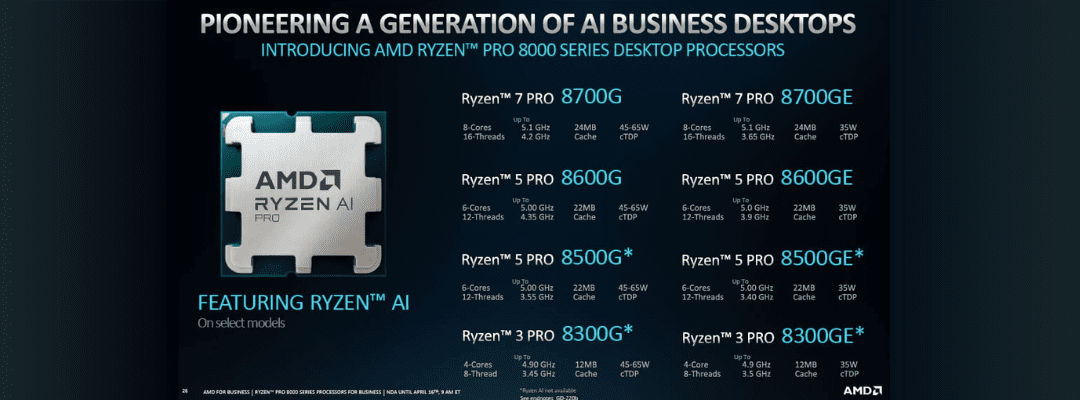
AMD has introduced a new line of Ryzen Pro processors: AI-powered Ryzen Pro 8000 for enterprise systems, Ryzen 8000G Phoenix desktop processors for desktop PCs, and Ryzen Pro 8040 Hawk Point for mobile devices also suitable for laptops and workstations. With this release, AMD became the first company to launch its neural processor (NPU), or AI accelerator in other words, for artificial intelligence processing on mobile and desktop options.
It is stated that mobile NPU processors show performance of 16 TOPS. This power surpasses the NPU competitor, the Intel Core Ultra Meteor Lake series, which has a performance estimated at 11 TOPS. AMD also outperforms its competitors in the overall AI functionality of the CPU and integrated graphics, with 39 TOPS compared to 34 TOPS of Intel chips. By the way, Intel has not yet released processors with an AI processing chip.
While the standard graphic interfaces of Windows and Linux are rather designed for regular users, the functionality of both systems is not limited by the features offered within the graphic interfaces. Many helpful features are somewhat concealed and can only be accessed via the command line interface. Today, we want to reveal one of these secrets and show you, how you can access Wi-Fi passwords for connected networks in both Windows and Linux via the command line.

Western Digital has released an SSD drive, its weight ranges from 12 to 15 kilograms and the capacity is 368 TB. To transport the Ultrastar Transporter the company created a special system on wheels.
The emphasis on security is continuing to gain recognition; thus, the implementation of efficient cybersecurity strategies widens its spread.
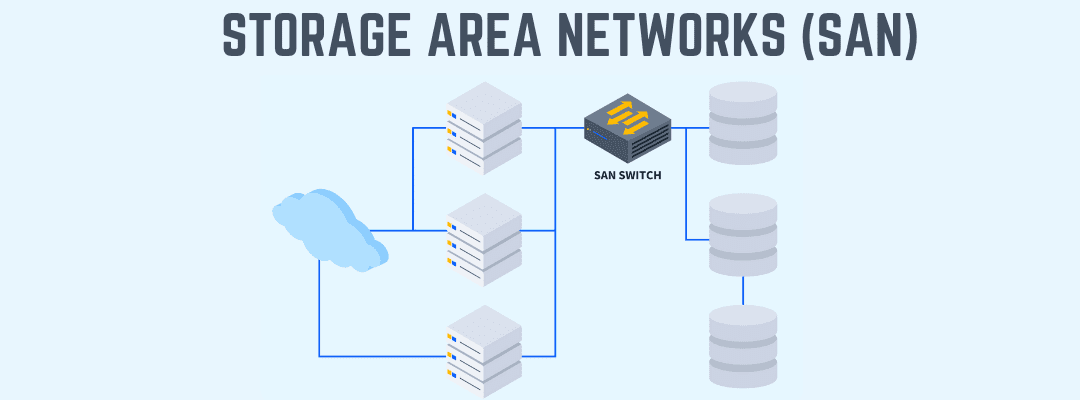
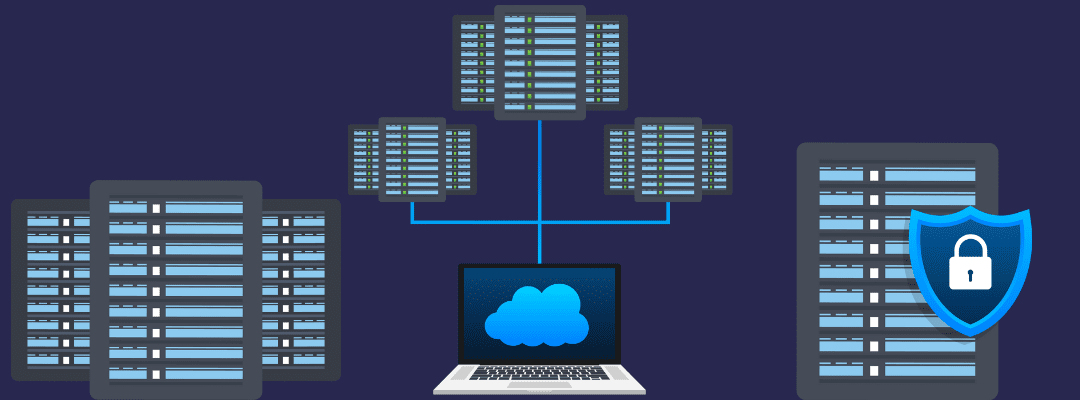
SAN refers to a storage area network and consists of creating a network of storage devices that can be used as a shared storage pool for multiple servers. SAN is one of the common solutions for delivering storage in network architectures that are spread nowadays and is considered a particularly potent and reliable option. Nevertheless, it’s also not free from pitfalls, so you have to consider them as well before opting for SAN as a solution for your own projects. In today’s article, we want to have a look at some essential weak spots of SAN to help you in your considerations.
Tackling file system metrics can be done in a variety of ways which we are not going to overwhelm you with in this article. Based on our practical experience in the field, we will give you some instructions about better monitoring. However, prior to this, you should deploy OS via Foreman. We highly recommend this system management tool for monitoring and configuring the servers both virtual and physical. This open-source tool has a great integration with config management soft that helps deploy apps, automate tasks, and even manage some changes.
Recently, a large-scale earthquake, the strongest in 25 years, hit Taiwan.
Since the country is one of the main suppliers of memory chips, many assume that the event will affect the pricing policy of manufacturers.
Most users when hearing “computer repository”, think about hard drives or USB drives. However, that is not actually relevant to repositories that are mainly divided into primary and secondary storage. If simply speaking then secondary storage is any non-voltage storage mechanism that guarantees the permanent storage of data.
Nowadays, probably the most important thing is the security of the available information because everything in our society evolves among data, its sharing, and usage. The distributed storage is a type of framework where information is not limited by one device or a certain place. Just on the contrary, the data is distributed across various locations, usually, it functions due to the network of connected machines or repository mechanisms.