What is a distributed component object model (DCOM)? Purpose and functionality
15:03, 14.05.2026
One of the most important early technologies in distributed computing was Microsoft's Distributed Component Object Model (DCOM). Although it's not as popular today as it once was, DCOM still plays a role in certain legacy systems and applications.
What DCOM Is
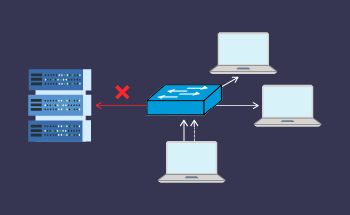
DCOM, or Distributed Component Object Model, is a Microsoft technology that enables software components to communicate over a network. It is an extension of the Component Object Model (COM), which is used for software interaction within a single computer. With DCOM, this communication can happen across multiple computers.
In simple terms, DCOM allows a software program on one computer to use the functions or services of another program located on a different machine as if they were on the same computer. This makes building large, distributed applications that share tasks across a network possible.
Purpose of DCOM
The primary purpose of DCOM is to enable interoperability between software components on different systems. Here are some of the goals it achieves:
- Remote execution
DCOM allows objects and their methods to be called from remote locations, which is ideal for distributed applications. - Scalability
Applications can be distributed across multiple servers or systems, improving performance and reliability. - Reusability
Developers can build modular software that reuses existing components by using COM components over a network. - Security
DCOM includes authentication and authorization features, making remote communication more secure.
DCOM was widely used in enterprise environments for remote data access, task automation, and client-server communication.
How Does DCOM Architecture Work?
DCOM builds on COM's core concepts but extends them to support communication across networks. To understand how DCOM works, let's first examine the architecture and main components involved.
1. COM Basics
Before diving into DCOM, it's important to understand COM. COM is a Microsoft standard for building software components that can interact with each other within the same computer. Each component exposes a set of methods through interfaces, which client programs can call.
COM components are registered in the Windows Registry with unique IDs (GUIDs). Clients can then instantiate these components and call their methods.
2. DCOM Layer
DCOM takes this model and adds a network layer that allows components to talk across machines. This involves a few additional steps:
- Marshaling and Unmarshaling
When a client calls a method on a remote object, DCOM converts the method call and its parameters into a format that can be sent over a network. This is called marshaling. On the server side, the data is unmarshaled, and the actual method is executed. - Remote Procedure Call (RPC)
DCOM uses Microsoft's Remote Procedure Call (MSRPC) to handle communication between the client and server. RPC acts as a middleman, carrying data from one machine to another. - Service Control Manager (SCM)
On each computer, DCOM relies on a Service Control Manager. This component helps locate and launch the required COM objects, whether they are on the local machine or a remote one.
3. Key Components in DCOM Architecture
Here are the main elements that enable DCOM to work across networks:
- Client Application
The program that requests a service or method from a remote COM object. - Proxy and Stub
On the client side, a proxy represents the remote object. On the server side, a stub receives the call. These help marshal and unmarshal data. - Object Exporter
This part of the server runs the component and responds to the client's requests. - DCOM Runtime
Both client and server computers have the DCOM runtime, which manages communication, error handling, and security. - Network Protocols
DCOM usually uses TCP/IP or named pipes to transport data.
4. Security and Authentication
DCOM supports built-in security mechanisms, including:
- Authentication levels to verify the identity of the caller.
- Authorization checks to control what the caller can do.
- Impersonation allows the server to perform tasks on behalf of the client
Administrators can configure these settings using Windows DCOM configuration tools (e.g., dcomcnfg).
Advantages of DCOM
- Integrated with Windows
DCOM is built into the Windows operating system, making it easy to use with Windows-based applications. - Object-oriented
Developers can use object-oriented programming principles to design reusable and modular components. - Rich security model
Offers fine-grained control over authentication and authorization.
Limitations of DCOM
Despite its early success, DCOM has several limitations:
- Windows-only
DCOM is tightly bound to the Windows platform, making cross-platform support difficult. - Complex configuration
Setting up DCOM in large networks can be complex and prone to errors. - Firewall issues
Because DCOM uses dynamic ports, it often struggles with firewalls and network security policies. - Outdated technology
In modern development, technologies like REST APIs, gRPC, or SOAP-based web services have largely replaced DCOM.
Modern Alternatives
As computing moved toward web-based and cross-platform solutions, newer technologies replaced DCOM. These include:
- .NET Remoting and later WCF (Windows Communication Foundation)
- Web APIs using HTTP/HTTPS
- Message brokers like RabbitMQ or Kafka
- gRPC, which is more efficient and supports multiple platforms
However, DCOM is still used in some legacy applications, especially in manufacturing, automation, and enterprise software that relies on older Windows systems.
Conclusion
The Distributed Component Object Model (DCOM) was a key technology in the evolution of distributed computing. It allowed software components to communicate across machines, offering a powerful way to build scalable, modular applications on the Windows platform.
Although its use has declined with the rise of newer technologies, understanding DCOM is still valuable—especially when maintaining or integrating with legacy systems. Knowing how DCOM architecture works helps IT professionals and developers appreciate the challenges and solutions of early distributed systems and how far we've come in modern software design.