What Is DNS Rebinding, and How to Prevent It
13:07, 14.05.2026
The Domain Name System (DNS) is one of the foundational technologies of the internet—it quietly translates domain names into IP addresses, allowing us to access websites and online services with ease. But this convenience also opens the door to a range of security risks if not properly managed.
One particularly dangerous exploit that targets the Domain Name System is known as DNS rebinding.
This article explains what DNS rebinding is, why it poses a serious threat to local networks, and how to protect your systems from this type of attack.
Understanding the DNS system
To grasp how DNS rebinding works and how to defend against it, it’s essential to understand the basics of the Domain Name System (DNS) and its role in internet communication.
At its core, DNS is a hierarchical naming system designed to resolve human-readable domain names (like example.com) into machine-readable IP addresses (like 93.184.216.34). Every time you open a website, check your email, or use an internet-connected app, your device performs a DNS lookup to find out where to send the request.
The mechanics behind DNS
When a DNS query is made, the request follows a chain:
- Local DNS cache is checked first. If the record exists and hasn’t expired, it’s returned immediately.
- If not cached, the request is sent to a recursive DNS resolver (often provided by your ISP or a public DNS service like Google DNS or Cloudflare).
- The resolver queries authoritative DNS servers up the chain, starting from the root DNS servers, until it gets the correct IP address for the domain.
The answer is then returned to the client and usually cached for a specified period known as TTL (Time to Live).
This infrastructure is fast and efficient, but inherently based on trust. DNS doesn’t authenticate the origin of the response unless security extensions like DNSSEC are used.
Why DNS is a common target for attackers
DNS operates at a low level of the Internet stack and is often overlooked in security audits. It offers attackers multiple opportunities to manipulate traffic, intercept data, or breach networks.
Although DNS was designed for functionality and speed, it wasn’t built with modern security challenges in mind. By default, DNS does not verify the integrity or authenticity of responses, making it susceptible to tampering.
Because DNS is such a fundamental and trusted part of network operations, attackers often exploit its vulnerabilities to intercept traffic, redirect users, or, in the case of DNS rebinding, trick browsers into making connections they normally wouldn’t allow.
DNS rebinding stands out because it targets internal networks using external websites, effectively turning a browser into a proxy to attack local devices.
Explaining DNS rebinding attacks
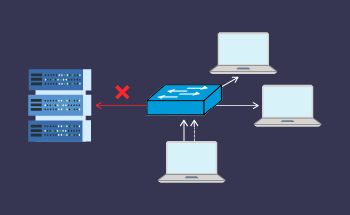
DNS rebinding is a technique that allows a malicious website to bypass a browser’s same-origin policy and interact with private IP addresses or internal services on the user's network.
How It Works:
- A user visits a malicious website controlled by the attacker, such as attacker-site.com.
- The website serves a script (typically JavaScript) that attempts to make requests to internal resources, like 192.168.1.1 (a local router).
- Normally, the browser blocks this due to the same-origin policy, which prevents scripts from one domain from accessing content on another.
- However, the attacker uses DNS rebinding to trick the browser. The DNS server for attacker-site.com initially resolves to a public IP that hosts the attacker's web content. After the script is loaded, the attacker’s DNS server changes the A record to point to a private IP, like 127.0.0.1 or a device on the local network. If the browser doesn’t re-check origin boundaries properly, it allows the script to make requests to the internal system, thinking it’s still talking to attacker-site.com.
This can give attackers access to router admin panels, printer configurations, IoT devices, or even internal APIs not meant to be publicly exposed.
Best methods to prevent DNS rebinding
DNS rebinding can be mitigated effectively using a combination of client-side protections, network settings, and application hardening.
Browser-Based Protection
Modern browsers have implemented some defenses, such as blocking access to localhost or enforcing stricter origin checks. However, these vary between browsers and aren’t always foolproof.
Users should keep browsers updated, avoid visiting untrusted websites, and use browser extensions or settings that restrict JavaScript or third-party domains
DNS Filtering and Rebinding Protection
Some DNS resolvers offer rebinding protection by blocking DNS responses that resolve external domains to internal IPs. These include OpenDNS (Cisco Umbrella), NextDNS, and Pi-hole (with custom configuration).
Web Server and Application Defenses
Internal services should never trust hostnames alone. Web apps and local APIs should validate the Host header and implement authentication even for local requests.
Additional practices include:
- Binding internal services to localhost or internal-only interfaces
- Requiring authentication for router or IoT admin panels
- Using non-standard ports (not a substitute for security, but it reduces exposure)
Network Firewall and Router Settings
These measures offer:
- Block outgoing DNS requests except through a trusted resolver
- Prevent internal devices from resolving or responding to external hostnames
- Use VLANs to segment sensitive devices from general user traffic
Disable or Restrict JavaScript Execution
On highly secure systems, you can block JavaScript or allow it only from trusted domains. This prevents malicious scripts from executing altogether.